Terug naar het overzicht
30 juli 2021
Microsoft voegt Safe Links phishing-bescherming toe aan Teams
Microsoft heeft de phishing-bescherming van Microsoft Defender voor de Safe Links-functie van Office 365 uitgebreid naar Microsoft Teams.
“In de kern biedt Safe Links verificatie van URL’s op het moment van klikken. Dit proces omvat het scannen van URL’s op potentieel schadelijke inhoud en deze opnieuw evalueren wanneer erop wordt geklikt door een gebruiker”, legt Girish Chander, Microsoft’s Group Program Manager van Office 365 Security, uit.

Gebruikers beschermen
Sinds het begin van de COVID-19-pandemie is het aantal gebruikers van zakelijke samenwerkingstools zoals Zoom en Microsoft Teams omhooggeschoten, aangewakkerd door de enorme verschuiving naar werken op afstand en de behoefte van bedrijven om (video)contact te houden met hun werknemers.
In maart 2020 bereikte Microsoft Teams 44 miljoen dagelijkse gebruikers. In april 2020 overschreed het aantal 75 miljoen, en deze brede pool van potentiële doelen is niet onopgemerkt gebleven door phishers.
In april 2021 had Microsoft ongeveer 145 miljoen dagelijkse actieve Teams-gebruikers. Dat is een enorm gebruikersbestand dat moet worden beschermd, en Microsoft komt op de plaat.
Safe Links phishing-bescherming in Microsoft Teams
Eerder dit jaar startte het bedrijf een nieuw Applications Bounty Program en heeft het bughunters uitgenodigd om de desktopclients van Microsoft Teams te onderzoeken op bugs. Vorige week hebben ze de reikwijdte van het programma uitgebreid met de mobiele apps.
Maandag maakte het bedrijf bekend dat de Safe Links-functie nu beschikbaar zal zijn voor Microsoft Teams – als de klanten ook Microsoft Defender voor Office 365 gebruiken.
Safe Links is sinds de introductie in 2015 een cruciale functie in Defender voor Office 365, zei Chander, en de ontploffingssystemen van Microsoft “detecteren bijna 2 miljoen verschillende op URL gebaseerde payloads die aanvallers maken om phishing-campagnes met referenties te orkestreren”.
Hij legde ook uit dat de keuze om URL’s te scannen op het moment van klikken te wijten is aan het feit dat aanvallers hun tactiek hebben ontwikkeld en nu goedaardige links verzenden van een omleidingsservice die kan worden gewijzigd om naar een kwaadaardige site te verwijzen.
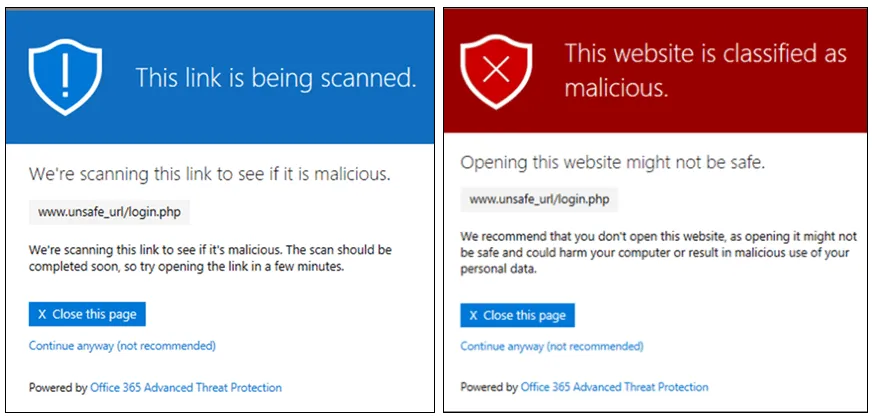
“Op het moment dat de e-mail door uw organisatie wordt ontvangen, lijkt de link ongevaarlijk en wordt de e-mail dus bezorgd. Na de klikinspectie zouden Safe Links de link echter bij aflevering hebben gecontroleerd en ervoor gezorgd dat wanneer op de link wordt geklikt, deze wordt doorgestuurd en geïnspecteerd. Als de link kwaadaardig is, krijgt de gebruiker geen toegang tot de site, en als de link onschadelijk is, mag de gebruiker doorgaan.”
Dergelijke koppelingen kunnen ook worden verzonden via gesprekken, groepschats en kanalen in Microsoft Teams, en kunnen ook worden opgenomen in documenten die via deze worden gedeeld.
Microsoft laat in de onderstaande video zien hoe Safe Links werken. Safe Links heeft volgens Microsoft al bijna 2 miljoen verschillende op URL gebaseerde payloads opgemerkt die cybercriminelen maken om phishing-activiteiten met referenties te organiseren.
Om Safe Links te gebruiken, moeten bedrijfsbeheerders een Safe Links-beleid configureren in de Microsoft 365 Defender-portal.
Bron: helpnetsecurity
Meer weten?

Gerelateerde
blogs
Tech Updates: Microsoft 365, Azure, Cybersecurity & AI – Wekelijks in je Mailbox.