Terug naar het overzicht
15 oktober 2021
Microsoft heeft een van de grootste DDoS-aanvallen ooit afgezwakt
De aanval was 2,4 Tbps
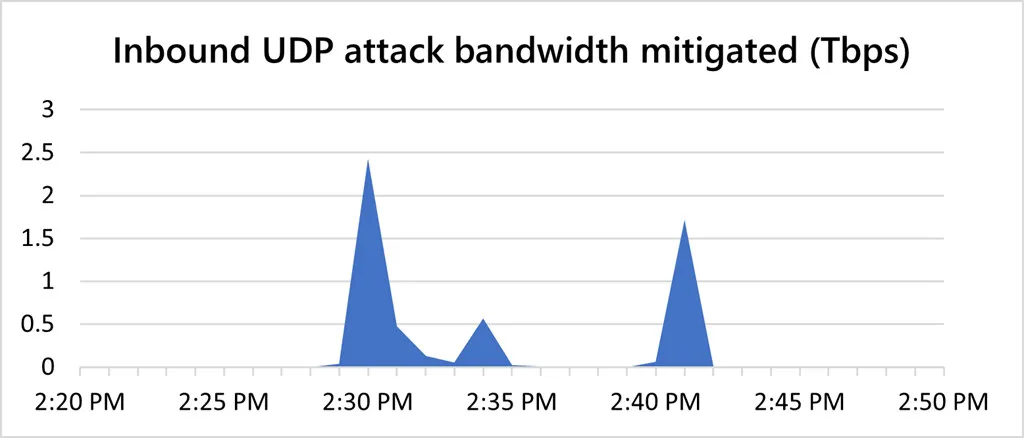
Microsoft zegt dat het in augustus een 2,4 Tbps Distributed Denial-of-Service (DDoS) -aanval kon afzwakken. De aanval was gericht op een Azure-klant in Europa en was 140 procent hoger dan het hoogste aanvalsbandbreedtevolume dat Microsoft in 2020 registreerde. Het overschrijdt ook het piekverkeersvolume van 2,3 Tbps vorig jaar gericht op Amazon Web Services, hoewel het een kleinere aanval was dan de aanval. 2,54 Tbps één die Google in 2017 heeft verminderd.
Microsoft zegt dat de aanval meer dan 10 minuten duurde, met kortstondige uitbarstingen van verkeer die piekten op 2,4 Tbps, 0,55 Tbps en uiteindelijk 1,7 Tbps. DDoS-aanvallen worden meestal gebruikt om websites of services offline te dwingen, dankzij een stroom verkeer die een webhost niet aankan. Ze worden meestal uitgevoerd via een botnet, een netwerk van machines die zijn gecompromitteerd met malware of schadelijke software om ze op afstand te besturen. Azure kon tijdens de aanval online blijven, dankzij het vermogen om tientallen terabits aan DDoS-aanvallen te absorberen.
“Het aanvalsverkeer was afkomstig van ongeveer 70.000 bronnen en uit meerdere landen in de regio Azië-Pacific, zoals Maleisië, Vietnam, Taiwan, Japan en China, evenals uit de Verenigde Staten”, legt Amir Dahan, senior programmamanager uit. voor het Azure-netwerkteam van Microsoft.
Terwijl het aantal DDoS-aanvallen in 2021 op Azure is toegenomen, was de maximale aanvalsdoorvoer gedaald tot 625 Mbps vóór deze 2,4 Tbps-aanval in de laatste week van augustus. Microsoft noemt niet de Azure-klant in Europa die het doelwit was, maar dergelijke aanvallen kunnen ook worden gebruikt als dekmantel voor secundaire aanvallen die proberen malware te verspreiden en bedrijfssystemen te infiltreren.
De aanval is een van de grootste in de recente geschiedenis. Vorig jaar heeft Google een 2,54 Tbps DDoS-aanval beschreven die het in 2017 heeft verzacht, en Amazon Web Services (AWS) heeft een 2,3 Tbps-aanval gemitigeerd. In 2018 weerde NetScout Arbor een aanval van 1,7 Tbps af.
Bron: TheVerge
Meer weten?

Gerelateerde
blogs
Tech Updates: Microsoft 365, Azure, Cybersecurity & AI – Wekelijks in je Mailbox.